Introduction
Monster agent, the element in charge of Monster Threat Hunting Cloud’s event log collection, is an optimized program that actively logs every kind of system event (e.g. process, network, system information). Monster agent works not only with Monster Threat Hunting Cloud, but also smoothly integrates with already in-use analysis systems through protocols such as syslog, kafka, and more. Event logs, including detection of systemic malicious code and abnormal network activity, can be applied to cover a wide variety suspicious activities.
Features
-
Active Event Log Collection
Monster agent is an optimized program for collecting event logs (e.g. process, network, file, registry events) needed for Threat Hunting. Though its basic setting is set to log and sort events according to its configuration, it can also collect and sort events according to external configuration files.
-
Real-Time Data Collection
Both collects in real time the system event logs needed for Threat Hunting and sends said logs to
Monster Cloud, or another integrable event log collection system. -
Event Blocks
Events, such as large files, registries, and network I/O generated by the system, are tracked in real time, condensed into required information, and neatly distributed into
Event Blocks.Each generated Event Block, following set-up preferences, is either saved as a TSV file or sent to an external system. Event blocks are composed of both summarized and detailed information regarding malicious activities. Event blocks are assigned unique key values, allowing for effortless tracing of procces-specific maliciousa activities.
-
System Linking
For smooth integration with existing analysis systems, collected event logs can be sent via protocols such as syslog and kafka. Following are examples of integrable systems:
- ELK (Elasticsearch, Logstash, Kibana) Stack
- Hadoop EcoSystem
- RDB (MySQL, MariaDB)
- Graph Database
- Casandra DB
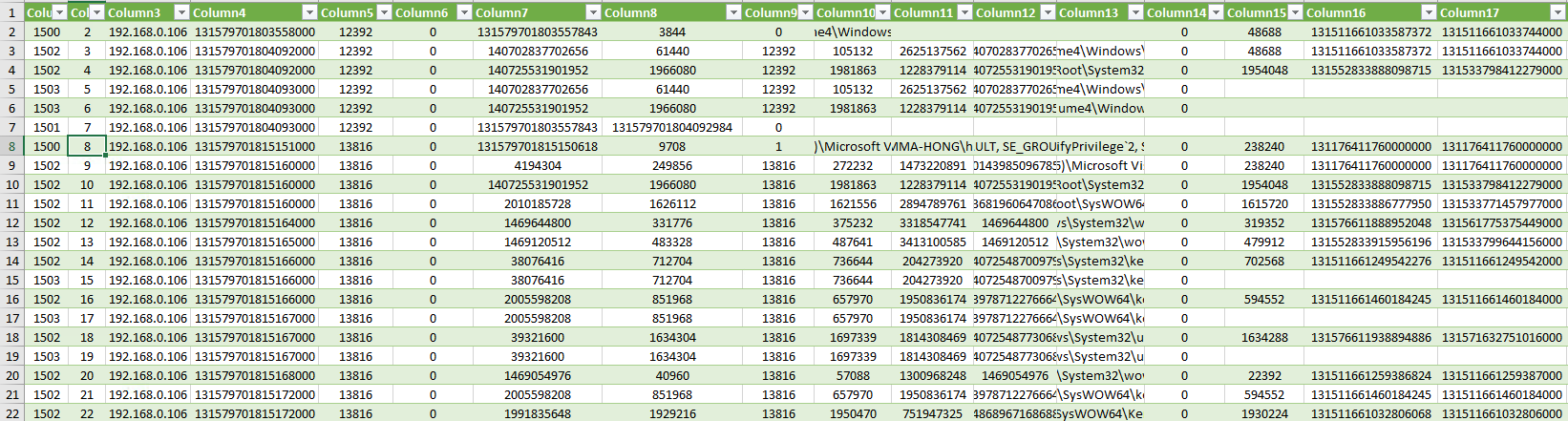
Event Examples
Events
Following are event logs collected via Monster Collector.
-
Event ID 1500: Process Create
Upon creation of a new process, process information (e.g. Creation Time, Process ID, Parent Process ID, Signature Informaton) is sent. Using information in the sent data, specifically command line, Current Directory, User, and Groups, all events during process creation can be identified and understood.
-
Event ID 1501: Process Exit
When a ‘process exit’ event occurs, the process information (e.g. process start and end time PID) is sent.
-
Event ID 1502: Image Load
Event log information is collected when a module is loaded from a process. The ‘Image Load’ event collects detailed information of the loaded module (e.g. hash, signature information, module name).
-
Event ID 1503: Image Unload
The event is sent when the module loaded from the process is unloaded.
-
Event ID 2500: File Event Block
Statistical information covering the start and end of a file event (writing, creatio, path change). The file’s name and its writing IO information is logged. In the case that the file’s name is altered after the start of an event, the altered name is logged and information on whether the file should be deleted or not is collected.
-
Event ID 2012: File Create
When a ‘File Create’ event occurs, the target file’s informaton (e.g. file name, file size, file creation time, file properties) is collected. Using ‘CreateOptions’ and ‘CreateDisposition’ in the events, detailed file information can be checked.
-
Event ID 2014: File Close
The file event log is collected upon termination of the event. As the file’s detailed information is sent upon file creation (Event ID 2012), the same information is not collected again in the ‘File Close’ event.
-
Event ID 2027: File Rename Path
Event information is collected upon renaming of the file path.
-
Event ID 2030: File Create New File
Event information is collected when a new file is created. This can be applied to detect unwanted leaking of local files as the file can be copied to a PNP device in the event of a change in the flag value of the ‘CreateNewFile’ event.
-
Event ID 3500: Netowork Connect
Event information is collected when a local system initiates an external connection. Detailed information regarding network connection is collected.
-
Event ID 3501: Netowork Accept
‘Network Connect’ describes the situation in which an external system communicates with a local system. The ‘Accept’ event information is collected after a local system accepts an external system’s connection request.
-
Event ID 4500: Registry Block
Provides statistical data covering the beginning to the ending of a registry event (e.g. registry key creation/deletion, registry value writing/deletion). The registry event sends the total number of events, as well as the entire registry’s path.
-
Event ID 4001: Registry Create Key
Event logged upon creation of a registry subkey. This event is useful for monitoring changes in registry key values characteristic of malignant code and other attack equipments.
-
Event ID 4002: Registry Open Key
Event logged when reading a registry key value.
-
Event ID 4003: Registry Delete
Event logged when a registry key value is deleted.
-
Event ID 4005: Registry Set Value Key
Event logged when a registry key value is altered. In the case of a change in a pre-existing registry key value, both the said key’s type and value are logged together.
-
Event ID 4006: Registry Delete Value Key
Event logged when a registry key value is deleted.
-
Event ID 4013: Registry Close Key
Event logged when a registry event terminates.
-
Event ID 6500: PNP Device Inject/Eject
Event logged for both the injection (connection) and ejection (connection termination) of a PNP device.
-
Event ID 7500: Raw Access Read
Event logged when a process begins directly reading a file from the disk. This event is useful both in detecting the deletion of MBR/VBR and other attacks similar to the hijacking of local accounts via acquisition of the registry SAM file, both of which are characteristic of malignant programs.
-
Event ID 8500: Host Info Block
System information (e.g. IP address, MAC address, Computer name, Local system accounts, Installed progrmas) is collected upon first execution of Monster Agent. When Monster Agent restarts, in the case of any changes in the system’s information, it collects updated information.
-
Event ID 9001: Process Access
Event logged when a process reads another process’s address space and begins a writing operation. This event is useful in the detection of attack tools similar to the ones used in reading memory information of processes (e.g.
Lsass.exe), frequently used inPass-the-Hashattacks for stealing the tokens of accounts to be used. -
Event ID 9002: Process Handle Duplicate
Event logged when a process duplicates another process’s handle for use in a third process.
Configuration Entries
A configuration file in json format is used for controlling Monster agent. As any settings not explained here are settings used locally by Monster agent, if at all possible it is recommended not to change them.
-
export setting
A required setting for linking with external systems. Changing the
enabledsetting value to1allows for collected information to be sent (kafka, syslog) or locally saved (tsv).{ ... "export": { "tsv": { "enabled": 1 }, "kafka": { "enabled": 0, "servers": "localhost", "topic": "monster", "acks": "0", "codec": "lz4", "partition": -1, "retries": 3, "max_msg_queue": 1000000 }, "syslog": { "enabled": 0, "server": "localhost", "port": 514 } } } -
Monster Event Filtering Entries
Monster Agent detects and collects all actions after the creation of a process. Collected events are nealty divided into blocks, able to be saved to a TSV file or sent to an external system. By using
trace_policy'a process’s events can be filtered and collected. Filters for collected events are in the same format as givn below, allowing forinclude[ing] orexclude[ing] of information such as process name, process path, filename extension, registry path, network destination IP, and PORT.{ ... "trace_policy": { "process_image_name": { "include": [], "exclude": [ "procexp64.exe", "taskmgr.exe", "dbgview.exe" ] }, "file_path": { "include": [], "exclude": [] }, "file_ext": { "include": [], "exclude": [] }, "registry_key": { "include": [], "exclude": [] }, "net_target_ip": { "include": [], "exclude": [] }, "net_target_port": { "include": [], "exclude": [] } } ... }
Conclusion
As the primary component of Monster Threat Hunting Cloud, Monster Agent collects in real time all system events needed for threat detection. Monster Agent can also be used independently, easily linking with other analysis systems. Through logged events…
- Can create detailed information on threats and process activities carried out by malignant code or attack tools
- Can detect the attack flow, such as the influx, execution, and spread, of an infected host system
- Can detect abnormal network traffic via the analysis of network traffic generated from the host
…among other activites that can be easily applied to.